Security video software platform
Architecture
The software architecture in the security field is the same as common software, which can be divided into stand-alone version, server version (CS/BS) and so on.
The stand-alone software is generally provided to users for free by equipment manufacturers such as network cameras and NVRs for supporting use.
Generally, the server version is considered from the perspective of data transmission, referring to the five-layer system structure of the computer network, the security software can be divided into platform support layer, intermediate service layer, public service layer, service construction layer, and application layer.
The platform support layer is composed of operating system platform, relational database, network communication protocol and so on.
The middle service layer is mainly various middleware used by the system, including data access middleware, object broker middleware, and message middleware.
The public service layer consists of various public services provided by the system, including graphics, reports, curves, permissions, alarms, streaming media services, and so on.
The service construction layer provides a consistent service model to upper-layer applications, which is mainly manifested as service interface, service registration, service search, service access, etc.
The application layer is mainly for various application modules for online monitoring, video monitoring, environmental monitoring, and comprehensive information query and display, including functions such as collection, calculation, query, analysis, streaming media, and related human-computer interaction interfaces.
Problem
In the security field, the stability of a single hardware product has nothing to do with the entire system. The stability of the software platform is closely related to the management scale of the entire security system. It is very important to provide the design and testing resources required for a stable and reliable security software product. The scarcity of test environments for large-scale video surveillance systems restricts the maturity and stability of management software.
Therefore, many management software are born out of specific large-scale security system engineering projects. From the actual project, after the practical test, it faces the broader market demand.
Charging model
The supporting stand-alone version is usually included by the hardware manufacturer, free of charge, and relatively simple in function.
Some of the server version platform software is charged according to the number of connected devices. On the other hand, some charge based on functional modules.
Provider
- Equipment hardware manufacturer
- AI algorithm company
- software company
- Project system integrator
- Party A needs customization
Functional module
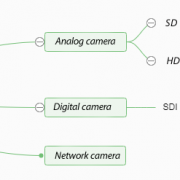
Intelligent analysis, access, matrix, storage, streaming media forwarding, client, networking gateway, electronic map, etc.
Common software platform
| No. | Software platform |
| 1 | Milestone |
| 2 | Digifort |
| 3 | Axxon |
| 4 | Nuuo |
| 5 | Geovision |
| 6 | Exacq |
| 7 | Aimetis |
| 8 | Genetec |
| 9 | Luxriot |
| 10 | SeeTec |
| 11 | Avigilon |
Development trend
- Intelligent
- Openness (access, third-party data integration, secondary development)
- Visualization, human-computer interaction



Leave a Reply
Want to join the discussion?Feel free to contribute!